Last month, various media outlets started reporting on distributed denial-of-service (DDoS) cyber attacks. These involved a cabal of hacked video surveillance cameras, digital video recorders (DVRs), routers and other Internet of Things devices.
These attacks are significant for a variety of reasons, not least their sheer size and scale. One of the most serious attacks reached 1.1 Terabytes per second (Tbps), with Octave Klaba, founder of OVH estimating the so called "Botnet" had the capacity to reach 1.5 Tbps. There were over 6,800 video cameras joined to the botnet.
“It’s getting huge,” Martin McKeay, a member of Akamai’s security intelligence team is quoted as saying. “You’re going to see brownouts, sections where a data center, an ISP, a region, may have so much traffic that it takes down that region.”

This is a seriously worrying trend for the Video Surveillance industry who have been touting the benefits of IP enabled and connected cameras for many years now. Security experts are also saying that this is a trend set to not just continue but grow.
Mckeay is quoted as saying "Now that we've seen a 600 gig botnet, we have to plan that within one to two years, those are going to become common,They may not be every attack, but we will see a dozen of them a quarter, we'll see a couple hundred of them a year. Now that people know those are a possibility, they're going to start pushing in that direction. They're going to make it happen."
Only back in June, security firm Sucuri uncovered another botnet of 25,000 Video Surveillance cameras from 105 countries attacking a small jewellery store website. The unnamed website was being assaulted by almost 35,000 HTTP requests per second, which actually increased to 50,000 HTTP requests at the height of the attack.
No-one as yet knows how such a large number of video cameras were hacked, however there was speculation they may have been exploited by a vulnerability that allowed remote code execution on DVRs from 70 different manufacturers.
All this raises some tough questions for manufacturers and installers of video surveillance cameras, as well as VMS suppliers. Exactly how can they prevent cameras becoming infected? Are they at least in part responsible for the thousands of vulnerable cameras that must now be out there “in the wild”?
It is not easy to know if connected hardware devices are infected. It is not possible to use antivirus software to scan for infections and often devices will show no sign of being infected or being used in DDoS attacks.
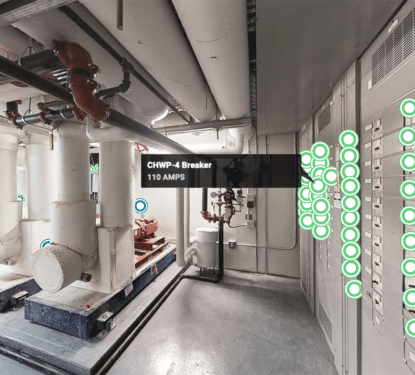
The fool proof method to protect cameras is never to connect them to the Internet in the first place. But this of course negates all the benefits we know the Internet of Things can bring to Smart Cities and Smart Buildings.
The video surveillance industry as a whole needs to act NOW to standardise best practice in cyber security and manufacturers must do a better job in educating installers about how to protect cameras and DVRs against attacks.
[contact-form-7 id="3204" title="memoori-newsletter"]