Last Decemeber, Nest, the smart homes firm owned by Google, was hit with a software glitch that has seen a number of devices turning themselves off and leaving owners in the cold. A botched software update caused the thermostat's batteries to drain or repeatedly switch on and off which meant it failed to heat homes or provide hot water to many customers.
"In some cases, this may cause the device to respond slowly or become unresponsive. We are working on a solution, which we expect to roll out in the coming weeks. In the meantime, performing a manual restart of the thermostat will help until a fix is put in place", said a Nest spokesperson. Nest has since rolled out a software update, which it claims to have solved the issue for 99.5% of affected owners.

This isn’t the first time a Nest bug has messed with users’ heating. Last march, a glitch with British Summer Time changed temperature settings at the wrong time, and two years ago, some users lost heat due to a miscommunication on Nest’s part about wiring requirements. Nest’s Dropcam security cameras also suffered an outage last autumn, leaving users unable to view their camera feeds.
Furthermore, Ph.D. student Sarthak Grover and fellow Roya Ensafi, two researchers from Princeton’s Center for Information Technology Policy (CITP), discovered that Nest thermostats were actually giving out the home zip codes of its users.
Nest acknowledged that this was a bug in its thermostat software and was of course not an intentional act, but other devices that the research team tested overshadowed the Google acquisition’s issue. The Ubi speaker, for example, was found to be sending voice chats and sensor readings over unencrypted HTTP, while the Sharx security camera transmitted video over unencrypted FTP.
“Some devices encrypt data traffic, but encryption may not be enough,” revealed the CITP via a blog posting. The researchers’ findings also revealed some very troubling data that privacy experts have warned about as more and more home appliances, baby monitors and security camera become “cloud aware”.
The more pervasive smart technology becomes the more at risk we are from bugs and faults in the system. This is not a new concept, but when you consider it in terms of the smart, IoT, connected world we are moving into, all manner of inconvenient to catastrophic scenarios could be conjured up.
Privacy aside, if we were to consider the initial Nest bug reported above in it’s worst case circumstances, we may lose heating for a few weeks while on vacation in the midst of a cold winter. In the scenario we might return to face an expensive and uncomfortable few weeks fixing frozen pipes and related damage, perhaps also the unfortunate fate of the cold on a pet left at home on an automated feeding system. Good home insurance would hopefully cover the former, and while the latter would be heartbreaking, it’s a far cry when you consider the potential ramifications of bugs in home security or safety devices.
[contact-form-7 id="3204" title="memoori-newsletter"]
Updates, patches and bug-fixes, are a language we are more used to hearing from the world of smartphone apps and computer operating systems. We’re used to the issues they fix, and the new issues they cause, in that setting. Such updates are a cornerstone of the complex programmes we use in the internet age, so will the IoT age mean we should expect those issues in the physical systems?
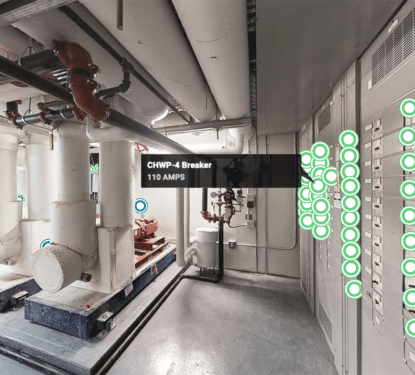
In August of 2015, it was reported that a bug in the firmware of an IV fluid pump allowed for hijacking, which could put patients lives at risk. TrapX Security released a white paper that purported the majority of American healthcare organizations are vulnerable to device hijacking. There are systems that could lock us out, or welcome intruders into our homes, or systems that control air quality or fire detection in large buildings, perhaps even systems that control important services across entire cities.
This is a situation where lives and property could be at stake. Updates must work. Developers have to take the extra time to fully test their code and allow extra time for beta cycles of their software. The alternative seems likely to be these potentially catastrophic effects to people, homes or whole cities – not to mention catastrophic financial loss for smart device developers, through class action law suits against them.