The workplace is changing in our ever more connected world. Mobile devices, the cloud, bring your own device (BYOD) and the Internet of things (IoT) have introduced a whole new style of computing, and are forcing businesses big and small to rethink what security needs to look like in order to protect the growing numbers of user devices and data. A shadow IT is quickly expanding in many, if not all, corporations and smart buildings in the digitally enabled world.
When software or hardware is being used within your company that you are not aware of, this is known as shadow IT. The term also applies to software and hardware being used that have not been approved. Reports suggest that almost all enterprises need to have a stricter BYOD policy to minimise security risks. As many as 72% of businesses who already have BYOD rules say their employees are using software or hardware that is not sanctioned by their IT departments.

"Everything with an IP address is a potential target, and by deploying a variety of IoT devices in the workplace, you've increased the number of targets for cybercriminals considerably," says Galindo. IoT devices send traffic to malicious network neighbourhoods, gather data or beacon-out even when they're not being used.
Hackers, malware writers, criminal gangs and even terrorists after an opportunity to steal data, disrupt a business or government agency can pounce, attacking an unpatched device or using the device's insecure infrastructure to move horizontally into a corporate network.
Put simply; the more connected devices, the more vulnerable a network is. "All devices, such as smart TVs, network attached storage (NAS) devices and wearable technology such as Fitbit do potentially expose a corporate network", says Dr Kevin Curran, Technical Expert at the IEEE, though he does point out that IoT devices are not equal, and that an infrequently patched Windows XP machine exposed to a network is much more of a threat than a webcam on the same network.
"Each device should be secure by default – it should only perform specific tasks and stop unauthorised activities from being carried out," says Amol Sarwate, Director of Engineering at Qualys. "Unfortunately, many developers don't have this mind-set in place from the start".
The reason is simple; IoT devices are cheaply made, with little thought for end-to-end security. "Many of the embedded devices simply do not have enough computing power to implement all the relevant security layers and functionality necessary," says Curran.
In security circles, BYOD is increasingly referred to as "Bring Your Own Danger" or "Bring Your Own Disaster”. However there are also numerous benefits to BYOD; for example, it's cheaper for the company, offers greater flexibility, and employees take much better care of their own devices than the do of company equipment. So the answer is not to scrap IoT, losing all the benefits that come with it, but instead to further develop, impose and maintain security infrastructure and protocol.
[contact-form-7 id="3204" title="memoori-newsletter"]
Making shadow IT less of a threat in the workplace requires some simple steps. "The first step is to create organisational rules and update network security infrastructure so that it can detect, and in some cases control, data transmitted to and from these devices", says Catalin Cosoi, Chief Security Strategist at Bitdefender. "Organisations should embrace a risk-management approach and reinforce the IT infrastructure and systems to restrict data access through firewalls, endpoint security solutions and proper policies, as well as monitor networks 24/7".
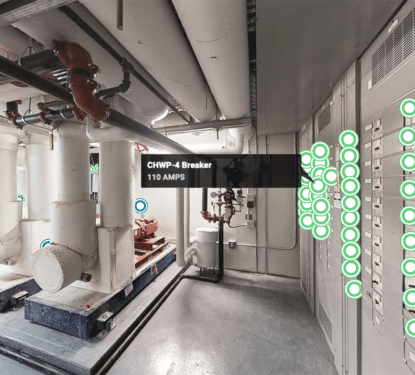
The issue is transferable into the smart building and the smart home, where data on individual behaviour can be stolen, or HVAC, lighting and even physical security systems can be accessed and controlled. As we see the expansion of The Internet of Things in Smart Buildings and The Transformation of BAS into the Building Internet of Things (BIoT) the urban environment will become a source of vulnerability in our smart world.
There is a strong desire for the digitally ambitious and forward-thinking companies, authorities and individuals to drive the IoT movement on, which by definition means more devices, more connectivity, and consequently more vulnerability. The current shadow IT security attitude suggests that we may have some high level security breaches before we create and enforce the necessary security measures.