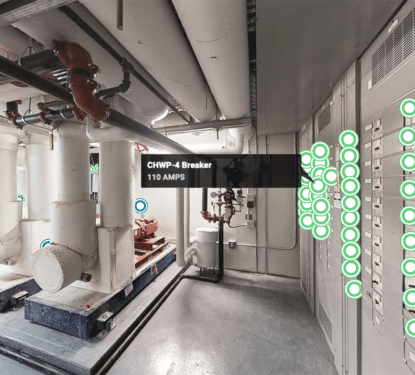
The Internet of Things (IoT) in smart buildings, homes, and cities has triggered a digital revolution for the built environment. Billions of sensors and devices now transmit real-world data to cloud computing systems in order to help us understand the physical world in quantifiable digital terms. IoT data is often sensitive in terms of privacy and security, however, and small IoT devices often lack the electrical or computational power to support sophisticated security protocols. This creates a “vulnerability of things” that could turn the IoT into a danger for society and undermine the promising digital revolution in the built environment.
“Over the coming years, billions of additional IoT devices and sensors are slated to come online. However, users now realize that these devices are not designed with cybersecurity in mind,” says Michel Girard, a senior fellow at the Centre for International Governance Innovation. “Minimum CPU and memory capacity are needed for users to manage and maintain IoT devices and keep them cybersafe. The breakneck speed of innovation, the intense competition between vendors to capture new markets, and the absence of safety and security regulations with respect to internet-related technologies have contributed to the current situation. As a result, every region of the globe has witnessed IoT cybersecurity breaches.”
Our latest assessment of the number of connected devices in operation in the commercial smart building’s vertical is for the installed base of connected devices to grow from 1.7 Billion in 2020 to just under 3 Billion by 2025 representing a CAGR of 10.8%. Meanwhile, malicious “PowerShell” scripts on IoT endpoints increased 1,000% in 2018 according to Symantec. Attacks on IoT devices tripled in the first half of 2019, according to CSO Online, who warn that the increased bandwidth of connected devices brought about by 5G will further increase IoT vulnerability. And, according to Cisco, the total number of IoT-based DDoS attacks worldwide will reach 15.4 million by 2023.
As connected devices play increasingly more pervasive and important roles of our lives, IoT cybersecurity issues become catastrophes waiting to happen. The unavoidable lack of computing capacity in these small, low-cost, low-power devices requires us to take an entirely new approach to cybersecurity, one that doesn’t depend on computing power but instead creates security while embracing the limitations of small but numerous IoT devices. That has become the focus of significant research in recent years as the growing problem begins to get the attention it deserves in academic and industry research.
“The things in the IoT environment are constrained due to the limited battery life, size, and computation, therefore, they cannot support the existing security solutions. The traditional cryptography algorithms and security schemes are insufficient for the ever-evolving IoT applications which require scalable and robust solutions,” explains a paper by Muhammad Usman of Chosun University in South Korea. “This requires the development of novel designs and architectures to effectively deal with the security and privacy issues suitable for the resource-constrained devices in the IoT. The resource-constrained devices in the IoT cannot utilize state-of-the-art encryption algorithms, thus the development of lightweight encryption algorithms is indispensable.”

One of the many companies striving to provide lightweight encryption for IoT devices is Polish startup Cyberus Labs. Founded in 2016, the Katowice-based startup has created a password-free solution designed to provide secure authentication and communication encryption using one-time-use tokens to authenticate both human users and smart devices. The cloud-based human-to-machine element of the authentication is built around sound, where a sonic signal is simply sent from one device to another, without the need for actionable credentials like passwords. Cyberus are set to launch a lightweight encryption solution in 2021 that will be available as a downloadable version on the Microsoft Azure Marketplace platform.
“Today, 80% of all data traffic between smart devices is unprotected. I think this will be one of the biggest challenges and one of the biggest investment opportunities in cybersecurity because we don’t have another choice,” says Marek Ostafil, cofounder of Cyberus Labs. “One of the biggest mistakes we’ve made was continuing using compromised authentication systems based on passwords in the world of IoT. Machine-to-machine authentication of billions of devices has been based on passwords. Right now there is a little bit of panic trying to figure out how to protect all this mess,” he added. “We’re not trying to build another wall of the fortress. We just eliminated the weakest element.”
Due to the large variety and heterogeneity of IoT devices and the security objectives of the applications using them, lightweight cryptographic algorithms for the IoT have proved challenging, however. Difficulties exist, both in terms of providing adequate security and in relation to the impact on device performance, necessitating significant compromises versus the cybersecurity levels we are used to in larger, more powerful devices. Such compromises may, therefore, limit the type of applications that we can apply IoT devices to in the long-term, at least until a secure lightweight solution is developed.
An experimental 2020 study, conducted by researchers from the University of Ulster and Manchester Metropolitan University, evaluated several legacy encryption/decryption techniques and compare them with more recently proposed lightweight techniques. The results clearly show that the hardware-oriented lightweight techniques perform significantly worse than the legacy techniques when they are implemented in software. Developers of IoT security systems, therefore, need to be mindful of the type of platform that a candidate encryption/decryption technique was developed for.
The IoT still represents the future, a future where the lines between the physical and digital worlds are blurred to create a data-rich, efficient, and intuitive connectivity-enabled new reality. However, unless we can solve the severe cybersecurity issues associated with the IoT, the continued proliferation of smart devices could have a severe impact on our built environment. We have waited too long to take this problem seriously but innovations by various companies now give us hope that the IoT future we have been promised can be secured.