As the global smart building movement marches on at increasing pace, it is sometimes easy to forget that many, building management systems hold potential vulnerabilities. The results of a one-year research project have revealed more than 100 flaws in building management and access control systems of the some popular vendors investigated.
In response, US Homeland Security has handed out a “perfect score” of 10.0, implying the most severe risk for the worst vulnerabilities identified by the research. Fixes and patches have been released, but the compelling results have underlined the widespread cyber security flaws that still exist in all smart buildings.
Just over a year ago, Gjoko Krstic, a researcher at industrial cyber security firm Applied Risk, began analyzing building management systems (BMS), building automation systems (BAS) and access control products from four leading vendors; Optergy, Nortek, Prima Systems and Computrols. Krstic focused his testing on specific products, the Computrols CBAS-Web, Optergy Proton/Enterprise, Prima FlexAir and two Nortek Linear eMerge products.
In response, US Homeland Security labeled Optergy’s Proton with the maximum severity in the industry standard common vulnerability scoring system. A score of 10.0 is a relatively rare event in this influential measure drew a quick response from the company. Although the advisory noted several other severe bugs, one of which was rated with a score of 9.9.
Krstic noted that many of the worst flaws required a “low level” of hacking ability to exploit and could be infiltrated to the deepest levels from a remote, presumably hidden, location. “By exploiting the vulnerability, it’s possible to shut down a building with one click,” he stated during a presentation in Amsterdam at Hack In The Box event in May. Adding, in a recent interview with TechCrunch, that the worst Optergy bug was “very, very bad” and “easy to exploit.”
Optergy appeared to be aware of the issue when approached by Krstic and soon released patches to fix the problem. The company’s president, Steve Guzelimian, said the company fixed the issues but wouldn’t confirm how many devices were affected, latest figures suggest the firm serves more than 1,800 facilities. “We fix everything brought to our attention as well as do our own regular testing,” said Guzelimian. The other vendors were also notified by Applied Risk, with the exception of Nortek, owing to their “notorious reporting process.”
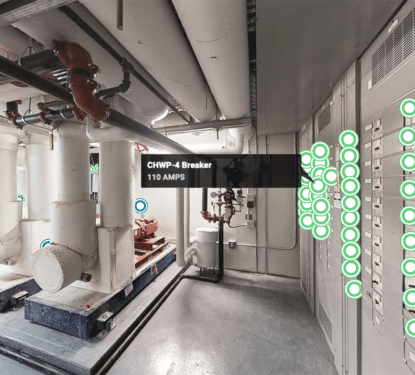
Krstic summarized his overall findings at SecurityWeek’s ICS Cyber Security Conference in Singapore, noting that an attacker could take advantage of these weaknesses to trigger alarms, lock or unlock doors and gates, control elevator access, intercept video surveillance streams, manipulate HVAC systems and lights, disrupt operations, and steal personal information. Highlighting that the flaws reveal that 10 million people and 30,000 doors at 200 facilities are already at the highest levels of risk from cyber attack - based only on the products investigated.

The ease of attack shown in Krstic’s research means attackers could be anyone, from a government-funded secret organization to a bored teenager, making attacks numerous and frequency, and against the biggest and smallest targets.
Krstic’s research does not tell us anything fundamentally new. No one in the smart building industry is betting their money on a 100% secure smart building management systems. Maybe we shouldn’t ever expect to be 100% cyber-safe in our smart buildings. After all, the PC market has managed to thrive despite comparable cyber-vulnerabilities.
Our buildings are not just cyber spaces however, where only our valuable data is at risk. The smart building is a cyber-physical human space where virtual attacks can cause very real and potentially harmful effects on the health and safety of occupants.
The current standard of cyber security in smart building systems is not enough to justify the risk. That risk grows exponentially as IoT adoption increases. Be it technological, political, or educational, a solution to this growing vulnerability problem must be found to avoid turning buildings, our historical “safe places,” into cyber-physical disasters.