“Don’t ever question if you will be hacked. You will be hacked,” proclaims IoTium CEO, Ron Victor, during Memoori’s Webinar last week, before describing a test anyone can try. “Open up a server on AWS and just watch. Within two hours, 55,000 people will try and hack into that box for some reason, just because it’s available.”
“Whether it’s a state sponsored terrorist attack, or some kid who just wants to prove he or she can do something, or a hacker trying to gain access to other subsystems. If it’s connected, people are going to try and hack it,” Victor states in no uncertain terms.
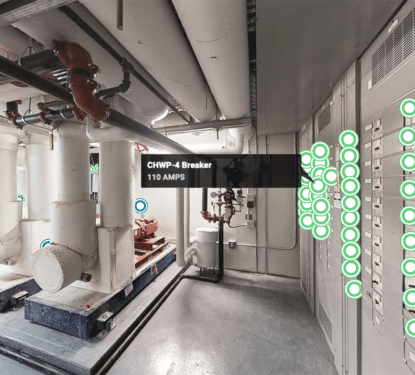
This is the problem faced buy smart buildings today as they open up more and more of their systems to the dangers of being connected. IoTium are a network infrastructure software company focused on the industrial internet of things (IIoT); the cyber security methods they are developing are based on layers and isolation. They are identifying and dealing with problems at the edge, meaning they never get the chance to cause real damage to the building and enterprise.
In a world increasingly full of connected lights, thermostats and toasters, it is near impossible to ensure that all your edge devices are not vulnerable to cyber attack. Unfortunately, many building owners and facility managers are not grasping why they need to invest in sophisticated security software to protect the office espresso machine or even the heating, ventilation and air conditioning (HVAC) systems.
“What people need to understand is that nobody wants their HVAC data, they want an entry point into your building and into your enterprise,” says Victor. “Hackers are using these types of OT systems to get into the building and gain access to more valuable systems.”
So we can protect our OT systems against a range of cyber threats active today by creating software that block those specific types of attack. Cyber threats are constantly and rapidly evolving, however, how can we future proof building security against hacking developments? One listener asked during the interactive webinar last week.
“What you can futureproof against is the ability to patch those hacks, that’s the virtualization of the edge,” Victor clarified. “In one example, 700,000 cameras got hacked because the camera vendor had left something open, the hackers then used those devices to create a DDoS attack. The vendor created a patch to solve the problem within four hours of the hack but the problem is how to deploy the patch to 700,000 cameras in 400 cities.”
So, ideally, at the click of a button, you would be able to send that patch out to every camera instantly. By solving the deployment problem you can futureproof against the full effects of the hack by quickly creating and deploying patches to affected devices. This is very useful to deal with a wide range of known hacking methods and many developments that may arise, but this is a reactive method once the hack has happened and some damage has been done. How can we prevent any losses from attempted hacks, now and in the future?

“In the same scenario, if our iNode architecture was in place, the DDoS attack, would never have been possible as the iNode only speaks to its mirror image on the other side,” Victor outlined. Going further, “if you were running a deep packet inspection (DPI) and a pattern recognition engine on the iNode, the moment an anomaly is detected, alarms would sound and data could be dumped at the edge before it causes problems,” thereby futureproofing against these type of threats.
Victor and IoTium are at the forefront of a movement to protect our increasingly connected world against cyber attacks with a multi-level defense. The iNode architecture helps prevent data going to the wrong place; DPI and pattern recognition can identify problems and acts as the first responder at the edge. If hackers do get through these layers, better deployment allows cyber security professionals to apply patches as soon as they can create them.
In the ongoing battle between hackers and cyber security professionals, something different was needed for cyber security to take the upper hand; some kind of out-of-the-box thinking that doesn’t fight fire with fire, but isolates the fire in order to prevent it doing further damage. IoTium and other leaders in this space seem to have taken a big step in that direction with these strategies.
Now the cyber security industry can focus on other big issue they face – educating convincing potential customers that only these sophisticated systems can truly protect their valuable assets against the range of cyber threats out there today and in the future.
“People often ask, what is the cheapest way to protect my system?” said Victor with some frustration. “That doesn’t make any sense to me! You’re protecting your enterprise building where 5000 employees are working, with all kinds of productivity worth millions of dollars, and you want to protect it with something worth 100 dollars. It makes no sense.”
[contact-form-7 id="3204" title="memoori-newsletter"]