Cybersecurity is a massive issue for smart buildings. Cybercriminals are relentless but we must accept them as a reality of connectivity. What we shouldn’t accept is that the IoT sector helps them by churning out insecure products that are picked up by unsuspecting owners and operators who may have limited IT and cybersecurity knowledge. Facilities management must get IT-smart as their buildings get IoT-smart if we are to avoid feeding the growing cyber threat with more cyber-insecure buildings.
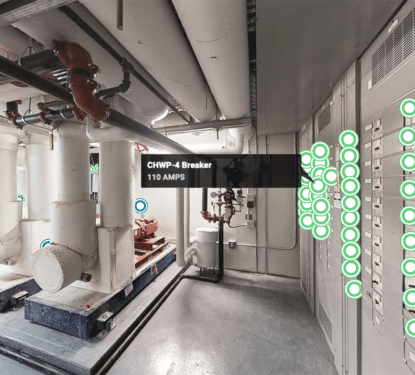
This is a new world for buildings. The traditional light bulb never had to share sensitive information with boilers or door locks, each operational technology (OT) just did its job independently and there was no talk of cybersecurity. Now smart buildings strive to interconnect every system through centralized building automation and control systems (BACS) to share data for increasingly powerful analytics to drive better energy efficiency, productivity, and occupant wellbeing simultaneously. BACS hold the key to every door in the digital building and often they are a part of the cybersecurity problem in smart buildings.
“A common factor among all building automation solutions available nowadays is the lack of satisfactory security mechanisms. Despite the recent introduction of security-oriented features such as encrypted communications, it is still relatively easy to maliciously interfere with the communications channels and bypass existing encryption and authentication mechanisms,” reads a 2022 paper by Vitor Graveto et al. and published in the Computers and Security Journal. “Additionally, BACS sensors and actuators are prone to physical tampering, and the remote management features are often outdated and vulnerable to more sophisticated attacks. Moreover, there is also a general lack of security monitoring and management tools for BACS.”
Popular building protocols for managing BACS include Modbus, BACnet, and KNX, each with their own cybersecurity benefits and issues. Modbus actually dates back to 1979 and the updated versions are commonly used with SCADA (Supervisory Control And Data Acquisition) for remote monitoring, control, and data acquisition. Modbus operates in a master-slave or server-client based model, master devices initiate all the queries such as transmission and monitoring, while the slave devices respond to those queries. This protocol structure makes Modbus vulnerable to relatively simplistic distributed denial-of-service (DDoS) attacks that overwhelm the system with requests, as shown in numerous studies.
“The attacks presented in the paper demonstrate that the Modbus protocol is highly insecure and care needs to be taken in networks where it is used. If a bad actor is able to run their own code either on a master itself, or anywhere between the master and the slave, then the communications between the pair should be considered compromised,” states ‘Fooling the Master’, a 2020 paper by Christopher Parian et al. “In both cases, the lack of security inherent in the protocol allows for bad actors to modify communications without the endpoints being aware of it. Additionally, the computational limitations of already installed hardware means that a more secure communications channel cannot be constructed for the insecure traffic to travel over.”
Some believe adding security to Modbus is unnecessary due to associated costs and legacy issues, as well as obsolete data models and chart recorders.
“Cyber security is a real threat, and we need to be concerned about it. But that doesn’t mean we have to engage in silliness. And that’s what I think about the effort to add security to Modbus,” says John Rinaldi is Chief Strategist, Business Development Manager and CEO of Real Time Automation. If you need to secure Modbus data use a Modbus/OPC UA gateway on every Modbus node. You can pass Modbus commands through that gateway, have them secured by the OPC UA infrastructure and turned back into OPC UA at the other end. Modbus with Security is an idea whose time has not come.”

This year, the American Society of Heating, Refrigerating and Air-Conditioning Engineers (ASHRAE) published an addendum for the BACnet protocol with new cybersecurity features. Secure Connect (BACnet/SC) is BACnet’s response to the criticism of its own cybersecurity failings.“Previous attempts to address these concerns went in a different direction than the IT community, ultimately frustrating efforts to gain acceptance,” writes ASHRAE in a whitepaper on the new update. “ BACnet/SC provides the means to create secure communications connections between automation devices both across the cloud, and within facilities.”
Released in November of 2019, BACnet/SC adds significant new security features, but more importantly, it focuses heavily on ease of integration with the existing infrastructure. Today, numerous approaches are used to secure BACnet infrastructure, but these solutions can be difficult to integrate for the limited IT teams in facilities management. If BACnet/SC is successful, it will become easier to create a secure and standardized building automation infrastructure that is fully compatible with existing BACnet deployments.
Other building protocols also continue to advance in security. KNX’s IP Secure protocol has become a new ISO Standard, EN ISO 22510, recognizing its capacity to protect IP communication between the KNX installations. KNX IP Secure extends the IP protocol to ensure that all data is completely encrypted, while also promising to protect user data, including data exchanged with the various terminals, against unauthorized access and manipulation by means of encryption and authentication. Both mechanisms can be combined and used in parallel to achieve maximum security in smart buildings.
With the ongoing progress in intelligent networking of buildings and infrastructures, including trending topics as sector coupling, smart grids, etc, there is a constantly growing number of data-driven use cases in KNX projects that rely on very sensitive data and require particularly high levels of security,” says Franz Kammerl, President of the KNX Association. “This is exactly where we start with KNX Secure, in which we expand our already very secure standard with additional security mechanisms to meet the highest IT security demands."
Modbus, BACnet, KNX, and other building protocols are all reacting to smart building cybersecurity issues but with different methods and varying levels of success. Such technological developments are absolutely necessary to reduce the threat of cyber attack but only if they are implemented, integrated, and maintained properly. Facilities management teams generally still lack the IT skills required to manage cybersecurity, poorly secured IoT devices still flood the market at attractive prices, and technology continues to increase in buildings despite cybersecurity concerns. Unless we enforce a minimum standard of cybersecurity, smart buildings will continue to be the low-hanging fruit for hungry hackers.
Regulation offers the opportunity to ensure companies adequately protect staff and customer data and privacy, or face a penalty. In the first half of 2020 alone, we saw a flurry of new legislation come into force in the US, with the California IoT Bill and the California Consumer Privacy Act (CCPA), in Japan through to the Telecommunications Business Law, and the IT-Sicherheitsgesetz 2.0, a draft IT Security Act bill in Germany. These legislative developments and many more build on the EU’s GDPR rules and will work alongside cybersecurity standards such as IEC 62443, ISO 27001, or NIST 800-53, which are gradually being embedded into new products, systems and processes.
“In the past, building devices and systems were isolated and faced fewer security risks. Over the years, buildings improved by providing interconnectivity, cloud connection and data analytics. With that came IoT-enabled devices connected to cloud services via the internet – opening the door to cyberattacks,” says Dr. Alina Matyukhina, Cybersecurity Manager at Siemens Smart Infrastructure. “The cybersecurity threat landscape is constantly changing, given the rapid pace of digitalization and technological progress in the building industry. But one thing is clear – a holistic approach to cybersecurity is essential.”